Introduction
For decades, Information Technology (IT) and Operational Technology (OT) operated in isolation—each serving distinct purposes. IT focused on securing data, while OT managed physical processes and industrial control systems. However, as organizations pursue digital transformation (DX) and integrate Industrial Internet-of-Things (IIoT) devices, these once-separate environments are converging. While this shift promises efficiency and cost savings, it also exposes critical infrastructure to unprecedented cybersecurity risks.
At Léargas Security, we’ve seen firsthand how the expansion of the attack surface has turned OT networks into prime targets for cybercriminals, hacktivists, and even nation-state actors. This case study explores real-world vulnerabilities in IT/OT convergence and provides strategic security recommendations.
Case Study: The High-Stakes Reality of IT/OT Cybersecurity
The Incident: A Ransomware Attack That Shut Down a Nation’s Fuel Supply
In May 2021, the Colonial Pipeline—the largest refined petroleum pipeline in the U.S.—fell victim to a ransomware attack. The attackers compromised IT systems, forcing a complete shutdown of OT operations. The impact was immediate:
- Fuel shortages across multiple states
- Panic buying at gas stations
- Significant financial losses for businesses relying on fuel transportation.
This attack was not an isolated incident.
These events highlight a dangerous reality: OT networks, once assumed to be protected by “air gaps,” are now exposed to cyber threats through IT interconnectivity.
The Root Cause: Why OT Is a Prime Target
The primary reason OT environments are being targeted? They were never designed with security in mind. Historically, OT relied on physical isolation for protection. However, modern demands for remote monitoring, automation, and efficiency have led to cloud integration and IT connectivity.
Key vulnerabilities include:
- Legacy Systems Without Security Patches
Many industrial control systems (ICS) run on outdated software that lacks modern security updates. Once connected to the internet, these systems become an easy target for cybercriminals. - Inadequate Network Segmentation
Insecure IT-OT integration allows lateral movement within a network. A breach in IT (e.g., phishing attack) can quickly spread into OT environments where it disrupts critical operations. - Lack of Security Awareness in OT Environments
Unlike IT, where cybersecurity practices are standard, OT teams are often unfamiliar with evolving cyber threats. Without proper incident response training, minor intrusions can escalate into catastrophic failures. - IIoT Devices Expanding the Attack Surface
The adoption of Industrial IoT devices means more endpoints to secure. Unfortunately, many of these devices lack robust security controls, making them an entry point for attacks.
Mitigating the Risks: A Proactive Security Strategy
To prevent devastating breaches like Colonial Pipeline, organizations must implement end-to-end OT security.
Here’s how:
- Enforce Network Segmentation
Implement strict firewall rules to separate IT and OT environments.
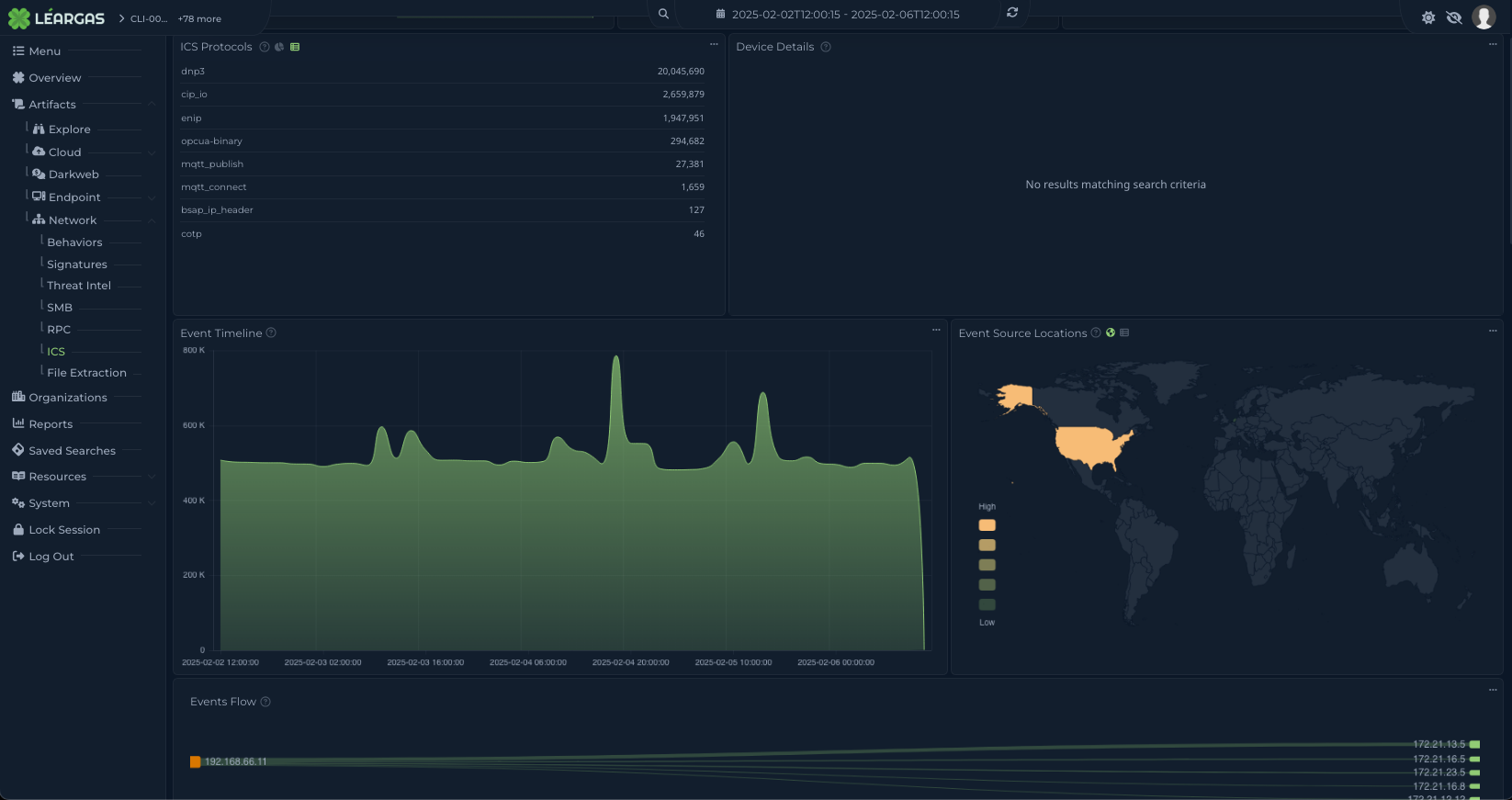
Use zero-trust principles to prevent unauthorized access between systems. - Conduct Continuous Monitoring and Threat Intelligence
Deploy XDR solutions (like Léargas XDR) to detect anomalies in real time.
Utilize behavioral analytics to spot unusual network activity before an attack escalates. - Regularly Patch and Update OT Systems
Work with OEM vendors to ensure critical updates are applied to legacy OT devices.
Establish secure remote access policies for patching sensitive infrastructure. - Train OT Personnel on Cybersecurity Best Practices
Conduct regular security awareness training for OT staff.
Implement phishing simulations to test readiness against social engineering attacks. - Implement Robust Incident Response Plans
Define clear action plans for responding to ransomware and malware attacks.
Conduct regular tabletop exercises to test readiness for IT-OT security incidents.
Conclusion: Securing IT/OT Convergence Is No Longer Optional
The rapid merging of IT and OT brings undeniable benefits, but it also creates a massive cybersecurity challenge. Organizations that fail to address these risks will face disruptions that extend beyond financial losses—they will impact public safety, national security, and daily life.
At Léargas Security, we specialize in securing IT-OT environments by providing advanced threat detection, network monitoring, and cybersecurity training. Contact us today to learn how we can help protect your industrial operations from cyber threats.