We are thrilled to announce that Patrick Kelley, CEO of Leargas Security, will be presenting at several prestigious cybersecurity conferences throughout the latter half of 2024. With over 30 years of experience in the field, Patrick is set to share his extensive knowledge and insights on various critical topics.
Continue readingExciting New Features in Léargas v0.1.0-beta.4
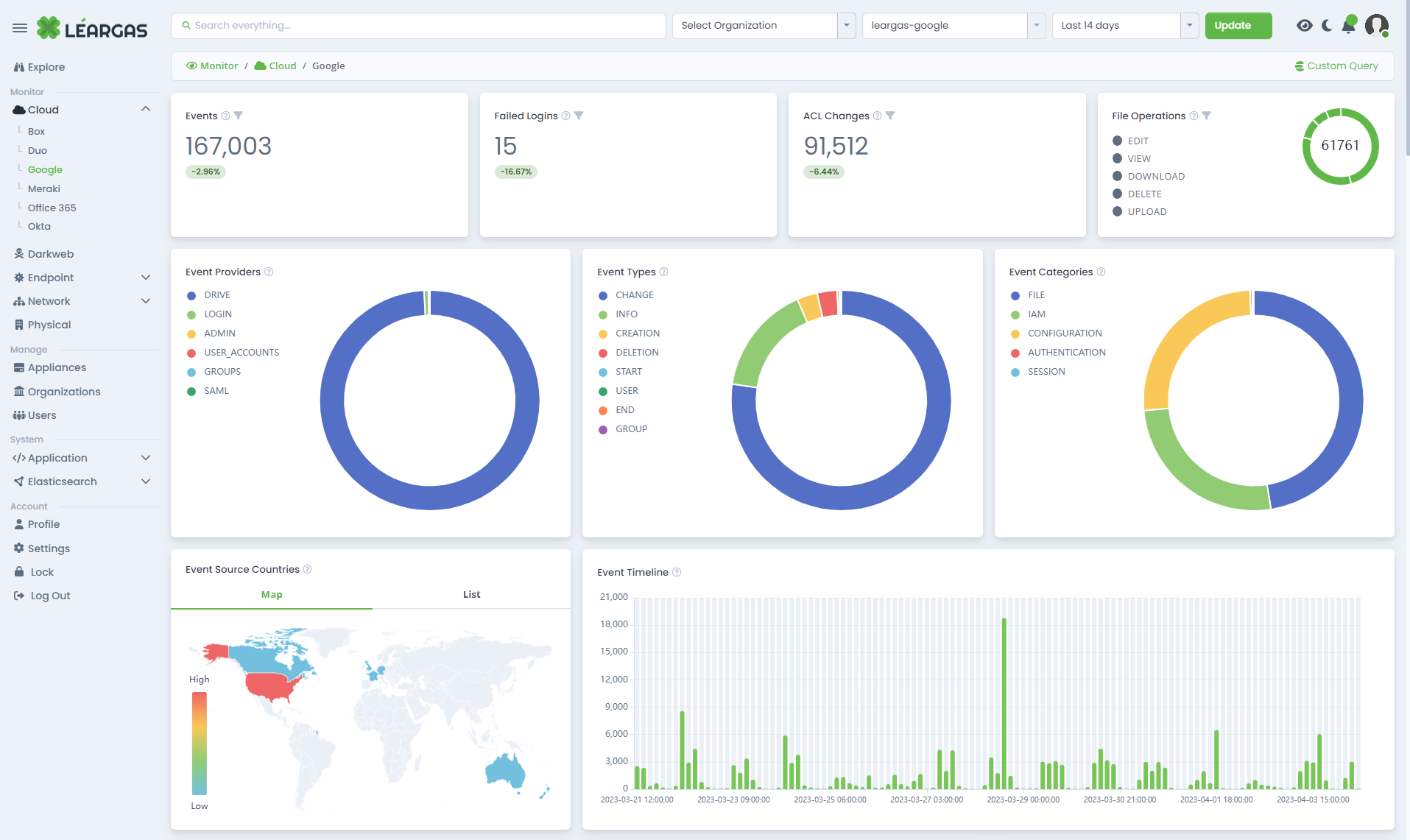
We are thrilled to announce the upcoming release of Léargas v0.1.0-beta.4! This update introduces several significant enhancements and new features aimed at improving user experience, security, and operational efficiency across the platform. Here’s a sneak peek into what’s new: Switching between devices has never been easier. With multi-device session support, you can effortlessly continue your sessions without any disruptions, providing convenient access to Léargas from anywhere. This feature enhances user experience by ensuring seamless transitions across devices.
Continue readingStrengthening the Fort: A New Era of Streamlined Cyber Incident Reporting
In the ever-evolving landscape of cybersecurity, the necessity for clear channels of communication and collaboration cannot be overstated. That’s why the recent announcement from the US Department of Homeland Security (DHS) is a crucial step forward for the community at large. On Tuesday, the DHS released an influential document that aims to revolutionize how federal agencies approach cyber incident reporting, ushering in a more harmonized and efficient system that stands to benefit critical infrastructure entities immensely.
Continue readingLéargas to participate in the Georgia EMC Technology Association’s Fall Meeting
In a fast-evolving world where technology stands as the backbone of numerous sectors, bringing together industry professionals to foster collaboration and growth is not just a necessity, but a mission to advance the industry further. The Georgia EMC Technology Association, an esteemed body with a focused approach to fostering excellence in the field of information technology, continues its long-standing tradition of promoting learning and collaboration with its upcoming Fall Meeting scheduled for September 20-22, 2023. This year, we are thrilled to announce Leargas Security as the proud sponsor of this promising event.
Continue readingLéargas XDR – Defending America’s Critical Infrastructure
In 2014, the pressing need for a comprehensive cybersecurity solution to the vulnerabilities faced by nearly 900 electric cooperatives was acknowledged by the U.S. Department of Energy (DOE). Understanding that the integration of Extended Detection and Response (XDR) solutions in electric cooperatives has become increasingly important in recent years, Léargas was driven to create a versatile and cost-effective platform. As these cooperatives digitally transform and adopt modern technologies, they also become more vulnerable to sophisticated cyber threats. These potential attacks not only pose a risk to the integrity of the cooperatives’ data, but also threaten the stability of the electrical grid that powers our communities.
Continue readingThe Crucial Role of Zeek-based Platforms like Leargas Security XDR in IT and OT Environments
The fusion of Information Technology (IT) and Operational Technology (OT) ecosystems is increasingly becoming integral in today’s enterprises. As the cyber threat landscape continues to evolve, posing intricate and sophisticated attacks, organizations are turning to advanced security solutions such as Leargas Security XDR. This potent platform, built on the robust Zeek framework, offers an all-in-one approach to securing IT and OT environments, providing vital insights and capabilities that help businesses stay ahead of potential threats. This article will delve into the significance of Zeek-based solutions like Leargas Security XDR with an emphasis on OT protocol analysis including DNP3, Modbus, and S7.
Continue readingRevolutionizing Energy Cooperatives: The Value of Leargas Security XDR
As the globe becomes progressively dependent on digital systems and automation, cybersecurity has evolved into a pressing issue for all organizations. This trend is not just applicable to major corporations or tech firms; it is equally relevant to entities like energy cooperatives. Given their key responsibility in delivering vital services to communities, these cooperatives cannot afford to overlook the importance of robust cybersecurity measures.
Continue readingLeveraging CIRCL’s AIL Framework and Leargas Security XDR Platform for Effective Breach Discovery and Management
As the digital landscape expands, so does the complexity and magnitude of cybersecurity threats. This shift has led to the development of sophisticated cybersecurity tools designed to detect, manage, and respond to potential security breaches. Two such tools making waves in the cybersecurity field are the Computer Incident Response Center Luxembourg (CIRCL) Analysis Information Leak (AIL) framework and the Leargas Security Extended Detection and Response (XDR) platform.
Continue readingThe Perils of Threat Intelligence Feed Poisoning: The Importance of Proper Curation and Validation of Artifacts
As organizations adapt to the ever-changing cyber threat landscape, they increasingly depend on threat intelligence feeds to remain informed about the latest malicious activities and safeguard their digital assets. These feeds provide real-time, actionable information on a variety of cyber threats, encompassing elements such as IP addresses, domains, malware hashes, and email addresses. However, the very resource designed to protect an organization can also become its Achilles’ heel when threat actors poison these feeds, potentially compromising networks and systems. In this blog post, we delve into the significance of proper curation and validation of artifacts as a means to counter the risks linked to threat intelligence feed poisoning.
Continue readingResponsible Usage of ChatGPT in Large Organizations: Ensuring Ethical and Secure AI Practices
Artificial Intelligence (AI) has made significant advancements in recent years, with ChatGPT by OpenAI emerging as one of the most popular language models. Its potential to enhance productivity and efficiency across a wide range of tasks is undeniable. However, as large organizations increasingly adopt this technology, it is essential to ensure responsible and ethical usage. In this blog post, we discuss the key points to consider when using ChatGPT in a large organization, focusing on security, reliability, and ethical concerns.
Continue reading