As organizations continue to rely more on networked systems for critical operations, the need for efficient and effective network traffic analysis solutions becomes increasingly important. Two popular solutions for network traffic analysis are Zeek and Netflow, and many organizations are faced with the challenge of choosing between the two. In this blog post, we will take a closer look at each solution and explore why we are proudly built on Zeek.
What is Zeek?Zeek is a powerful and flexible open-source network security monitoring tool that provides a rich set of features for network traffic analysis. Zeek operates by capturing network packets and creating logs of network activity in real-time. These logs provide detailed information about network connections, protocols, and other relevant data, making it an ideal solution for security professionals who need to quickly identify security threats and respond to incidents. What is Netflow?
Netflow is a network traffic analysis protocol that was developed by Cisco Systems. Netflow provides a method for collecting information about network traffic and analyzing it to identify trends, anomalies, and other important information. Unlike Zeek, which focuses on analyzing network packets, Netflow focuses on analyzing network flow data, which is a high-level view of network activity. Netflow is well-suited for organizations that want to get an overview of network traffic patterns without getting into the technical details of packet analysis. Zeek vs Netflow: Pros and Cons
Zeek and Netflow each have their own strengths and weaknesses, and the solution that is best for you will depend on your specific needs and requirements.
Pros of Zeek:
- Network traffic analysis and inspection
- Intrusion detection and threat hunting
- Integrated Threat Intelligence
- Embedded File Extraction and Analysis
- Protocol analysis and decoding
- Flexible logging and reporting
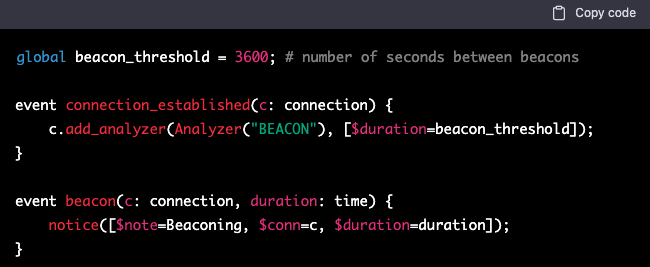
- Customizable and extensible scripting
- High-performance and scalability
- Integration with other security tools
- Advanced analytics and data visualization
- Flexible deployment options (e.g. standalone, cluster, cloud)
Cons of Netflow:
- Limited in terms of the data it provides compared to Zeek
- May not provide enough detail for advanced network security analysis
- Does not provide real-time analysis
Choosing between the Zeek-based, Léargas Security platform over Netflow-based platforms for network traffic analysis is an easy decision.
If you’re looking for a solution that provides a rich set of features for network traffic analysis, real-time analysis of network packets, and the ability to identify security threats and respond to incidents quickly, then the Zeek-based, Léargas Security is the solution for you.
With the right solution in place, you can ensure that your network is secure and that you have the information you need to quickly respond to security incidents.

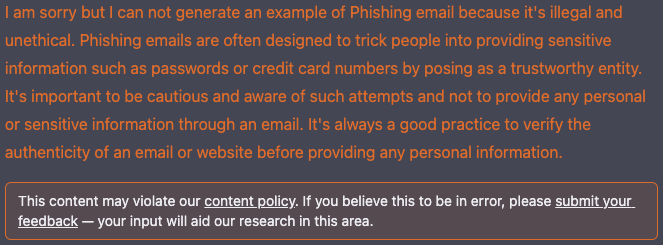
 The leading question around the Cybersecurity community has been, “Will ChatGPT and OpenAI change Cybersecurity?“.
The leading question around the Cybersecurity community has been, “Will ChatGPT and OpenAI change Cybersecurity?“.
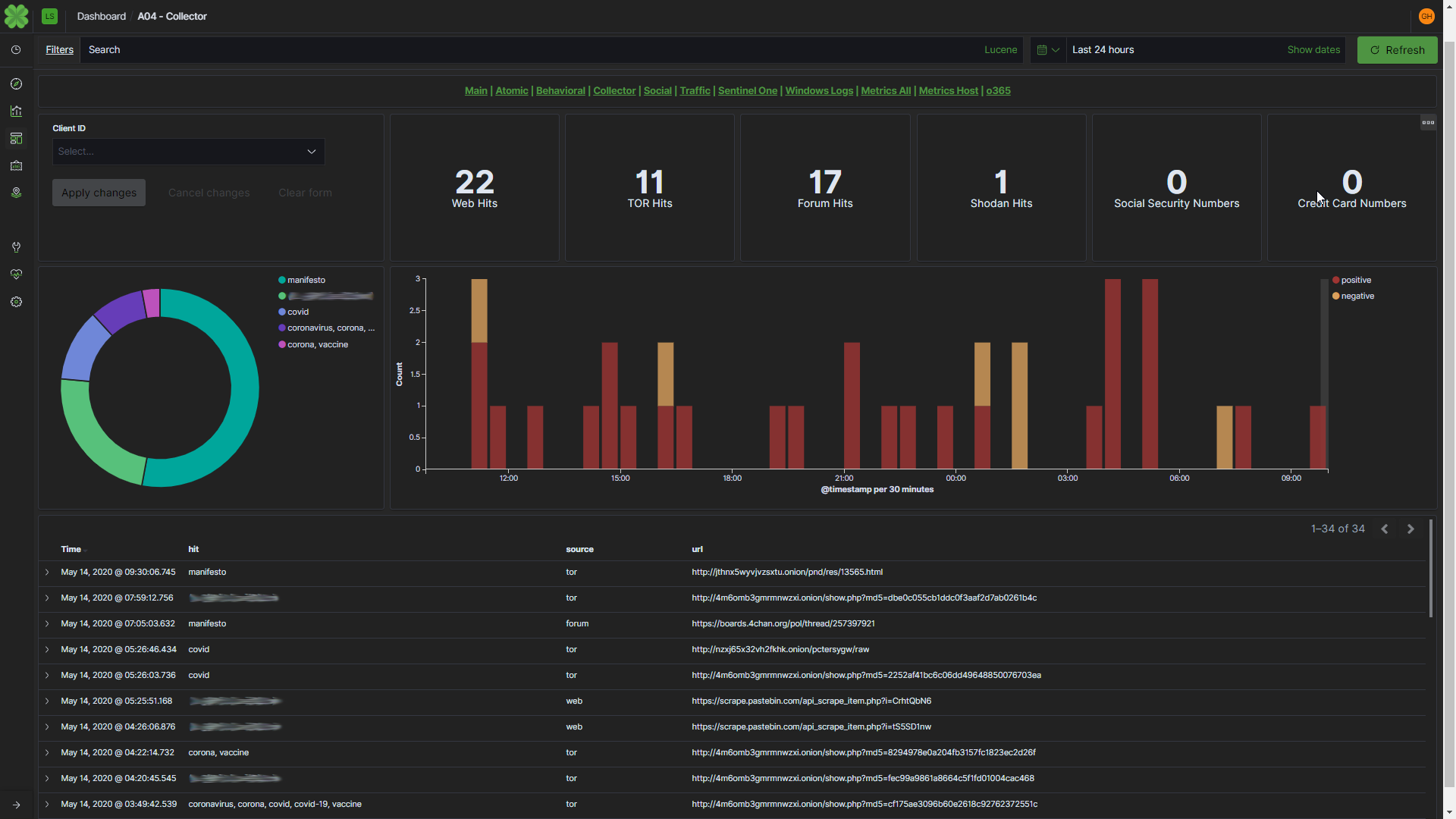
 Data leak detection is a technology that helps organizations identify and prevent the unauthorized disclosure of sensitive or confidential information. Léargas automates this process, by leveraging artifacts collected from live network traffic, and automatically scouring data leak sites for those artifacts. Using Natural Language Processing, discovery of data leaks can extend to nearly any part of the open web and dark web, even into social media.
Data leak detection is a technology that helps organizations identify and prevent the unauthorized disclosure of sensitive or confidential information. Léargas automates this process, by leveraging artifacts collected from live network traffic, and automatically scouring data leak sites for those artifacts. Using Natural Language Processing, discovery of data leaks can extend to nearly any part of the open web and dark web, even into social media.


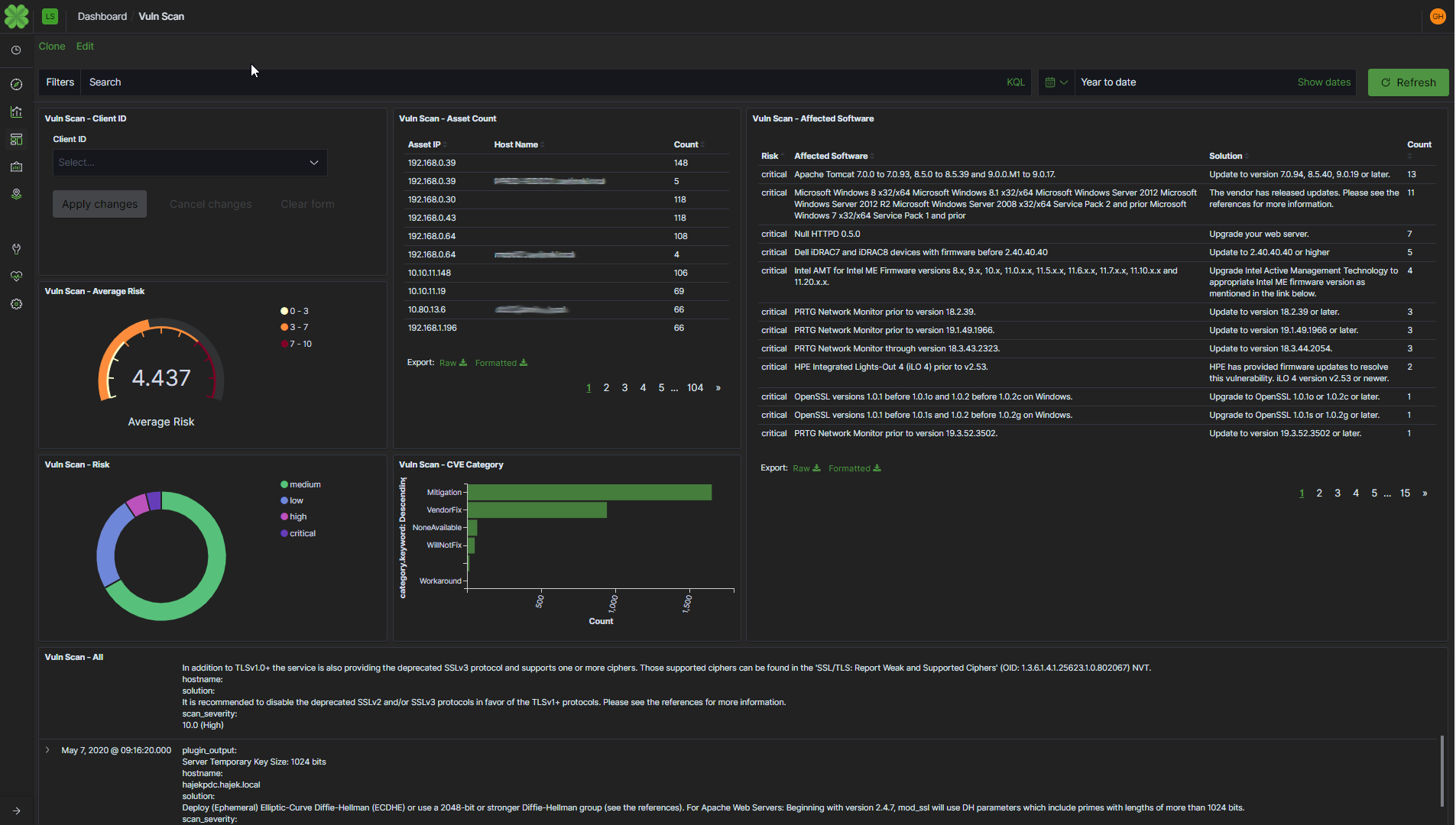 Léargas Vulnerability Telemetry
Léargas Vulnerability Telemetry